How Investigators Use OSINT to Track Down IPTV Pirates
 Measures to tackle online piracy are often described as a game of whac-a-mole, in this case a game where pirates get bashed on the head only to pop up somewhere else – supply of movies, TV shows, live sports and music intact.
Measures to tackle online piracy are often described as a game of whac-a-mole, in this case a game where pirates get bashed on the head only to pop up somewhere else – supply of movies, TV shows, live sports and music intact.
From the average pirate’s perspective, the game is completely pointless – futile even. But for anti-piracy groups all around the world, engaging pirates in this irritating game is an important form of disruption. It’s the next best option given the 0% chance of killing all piracy and the greater than 0% chance they’ll switch to a legal service.
The massive proliferation of pirate IPTV services in recent years is a big problem for many rightsholders. They’re able to annoy a few with ISP blocking but behind the scenes they’re also shutting a few down here, and a few down there. How they do that is rarely for public consumption but documents made available to TorrentFreak shine a little light on the basics. But first a short primer.
OSINT – Open Source Intelligence
At the lowest level, OSINT is available to all by simply gathering and processing data found using a search engine. In the world of OSINT, however, search engines represent only a handful of tools in an extremely large toolbox. When these tools are combined and harvested data is processed effectively, it’s possible to obtain worrying levels of information on all but the most hardened targets.
The screenshot below shows just some of the tools listed by OSINT Framework but even this selection barely scratches the surface, especially if we include the associated skills needed to effectively gather and then correlate data.
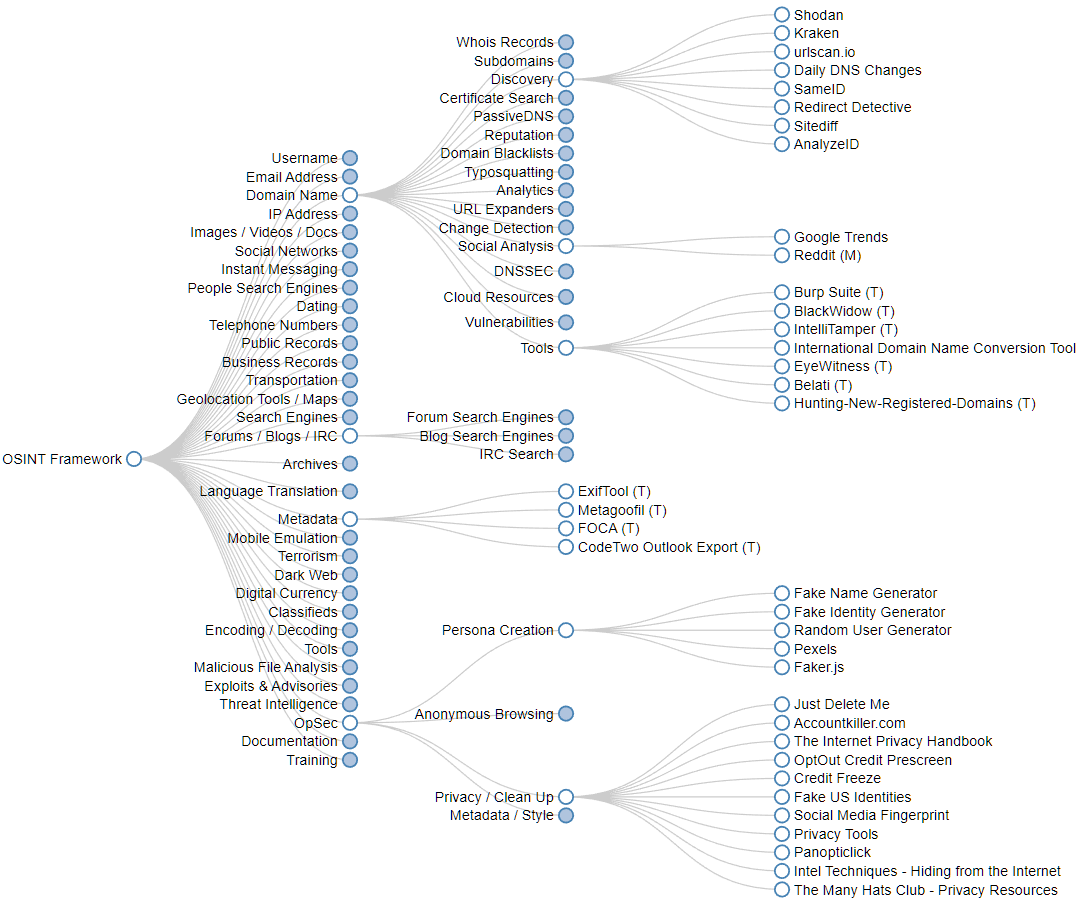
When it comes to online anti-piracy investigations, OSINT tools and techniques can feel almost tailored for the task at hand. Any single piece of information about a site operator (such as a domain name, IP address, or email address) has the potential to expose a person’s online footprint. And since today’s online lives tend to be inextricably entwined with those enjoyed offline, it’s not hard to see where things can end up.
IPTV – Investigation Examples
In 2021, a project funded by the European Union/EUIPO gave a presentation in Asia that focused on the investigation of various players in the illegal IPTV ecosystem. The chart below lists everything from content providers, aggregators and developers, to money and ‘subscription mules’ – otherwise known as ‘resellers’.
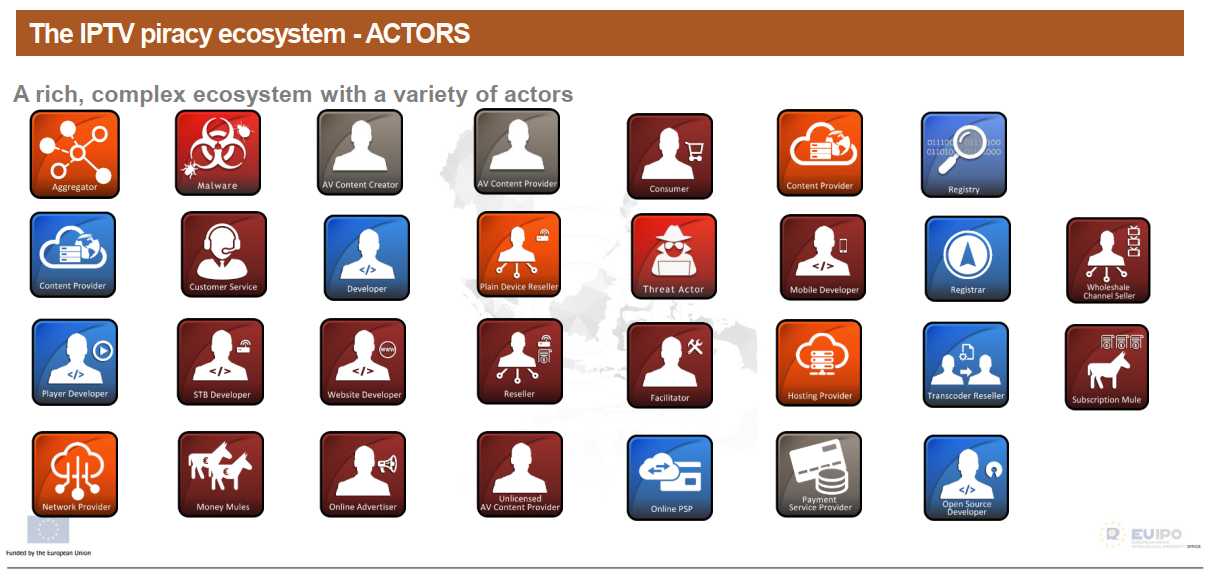
One interesting section concerns server devices known as ‘transcoders’. Video streams are sent to these servers from external sources (live TV or IP streams) and then transcoded/converted into multiple streams for delivery to multiple users’ viewing devices, usually via other networking infrastructure.
The specific model mentioned in the slides (TBS8520) can be managed using a system called ‘Kylone’ which is accessible using a web browser. So, when the investigators searched for ‘Kylone’ using ‘ZoomEye‘ (an OSINT search engine for the ‘Internet of Things’) the system was able to provide information on more than 141 transcoders. (Note: Using Shodan is also an option)
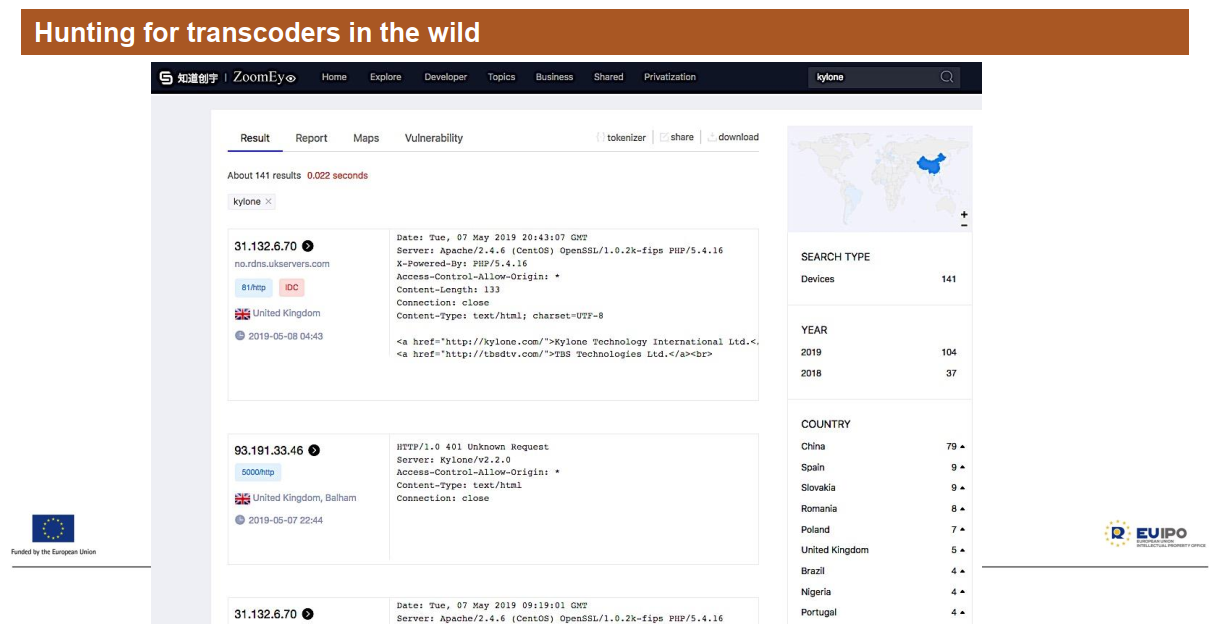
Knowing where these servers are located is useful information for obvious reasons. An IP address (such as the first result in the chart above) has the potential to lead to a hostname or even a physical location using simple tools.
(Note: Hosting companies, including the one in the example, may have no idea a customer is involved in illegal activities and, in any event, the customer in question is probably long gone)
Ulango.TV: A Lesson in How To Get Caught
In January 2020, we discovered that the Alliance for Creativity and Entertainment had taken down Ulango.tv, an ‘IPTV solution’ offering thousands of live channels through an app. As far as we’re aware, ACE still hasn’t claimed responsibility but there’s no doubt they took it down or were involved in some way.
According to slides in the EU/EUIPO presentation, cracking the case was simplicity itself. Armed with the site’s domain name (ulango.tv) and a WHOIS service, the investigators were able to obtain an IP address and the details of the company hosting the server.
Next they created a map of the ulango.tv site using this tool, which produced a list of external sites the .tv domain linked to. That included a link to a Twitter account and another piece of the puzzle.
Turning then to Hunter.io, a very powerful service for email-related investigations, they searched for the Ulango.tv domain and found an email address connected to it. At this point they appear to have used a little bit of skullduggery.
Using the services Fakemail and Fake Person Generator they made an account on Ulango.tv with bogus information. Obviously, there are reasons investigators don’t want to expose themselves in situations like these since that could be counterproductive.
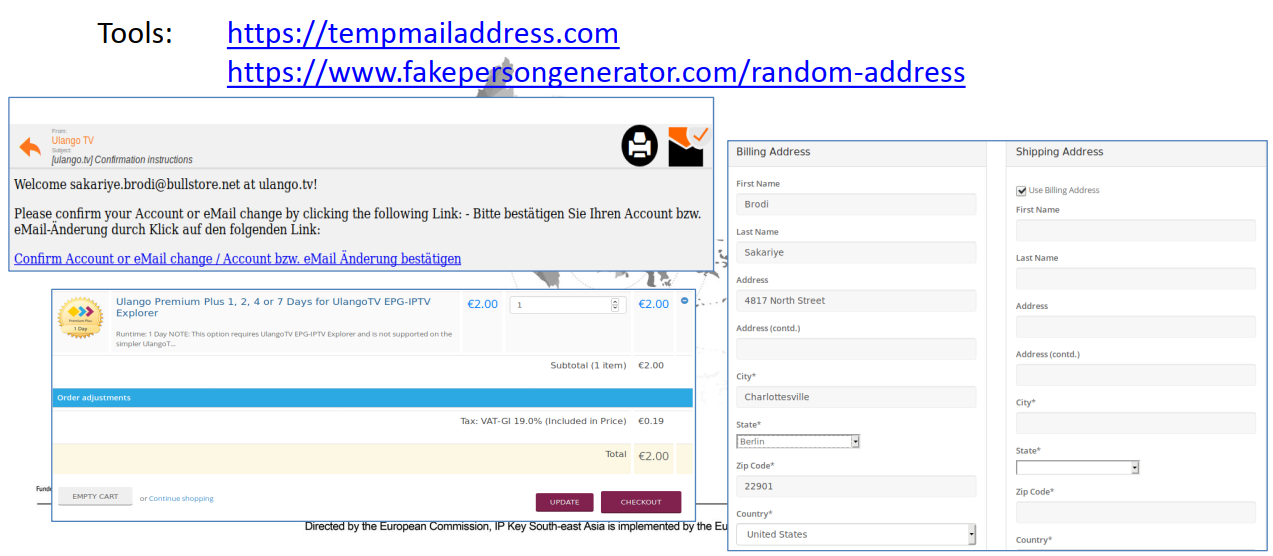
As the slide shows, the next step was to move towards a purchase of the site’s premium service for the princely amount of two euros. Then, after clicking the ‘checkout’ button, they were given the option to pay by credit card or bank transfer.
Out of necessity an IBAN number was provided along with the name of the account holder, a name that had also appeared earlier in the investigation. It wasn’t difficult but it appears to have been effective.
IPTV Investigation Using Multiple Tools
Finally, the slides detail another investigation but since our checks indicate the platform is still live, we don’t intend to name it here. Instead, we’ll simply walk through the steps.
Using the site’s domain name, investigators used Viewdns.info to conduct a WHOIS search to reveal the name of the domain registrant. Armed with that name they conducted a reverse WHOIS search, which displays other domains registered by the same person.
In total, these steps turned up a name, an email address, a potential physical address and 10 additional domains, mostly connected to pirate IPTV services.
The next step was to load up the main domain and view its source using a regular browser. By searching that source code for the term ‘UA-‘, they were able to find the site’s Google Analytics ID. By conducting a Reverse Google Analytics search, other sites using the same ID were revealed and connected to the first site.
Then it was a matter of attempting to pay for a subscription at the first site and noticing that payment was being processed by another. That site was (and still is) presented as a legitimate business and as such is incorporated as a limited company in the UK.
All limited companies in the UK have a listing at Companies House (another great OSINT resource) and a search there gave up the name of the director (a foreign national), a date of birth, and an address in London. The latter is a known virtual office and the home of many people who prefer not to give up their real address.
At this point the slides reveal no more so it’s unclear whether the investigation ended there or is still ongoing. The sites in question appear to be up so for educational and entertainment purposes only, we’ll see if the case can be cracked using the incredible capabilities of Maltego and Spiderfoot.
These tools allow users to automate their OSINT queries and investigations but such a short description does them both a huge disservice. They both have a free option so there’s no excuse for not giving them a try, preferably in a virtual machine and certainly behind a VPN, especially in the case of the latter.
From: TF, for the latest news on copyright battles, piracy and more.










Comments